The failure of a kinetic plot against a specific ethnic or religious enclave is rarely a matter of chance; it is the result of a friction point where radical intent meets the hardening of urban infrastructure. When security officials describe an attempt to target the "heart" of a community, they are referencing a strategic calculation by an adversary to maximize psychological disruption by striking a high-density, high-symbolism node. Effective defense against these asymmetric threats relies on three distinct variables: signal detection in non-permissive digital environments, the physical hardening of soft targets, and the reduction of response latency by law enforcement agencies.
The Mechanics of Target Selection and Symbolic Value
In the context of urban security, a "target" is not merely a physical location but a nexus of social and cultural capital. Adversaries prioritize locations based on a cost-benefit analysis that weighs ease of access against the "shock value" of the strike. The New York Jewish community represents a complex security environment because its vital organs—synagogues, schools, and community centers—are deeply integrated into the civilian fabric.
The "heart" of a community, in tactical terms, is the point of maximum density. Striking these points serves a dual purpose for the perpetrator:
- Kinetic Efficiency: Maximizing casualties per unit of effort.
- Psychological Cascading: Creating a persistent state of hyper-vigilance that disrupts the normal economic and social functioning of the targeted group.
The vulnerability of these sites often stems from their primary mission of being open and welcoming. This creates a "Security-Utility Paradox" where the measures required to ensure absolute safety (walls, armed checkpoints, biometric screening) inherently degrade the communal purpose of the institution.
Digital Signal Detection and the Intelligence Gap
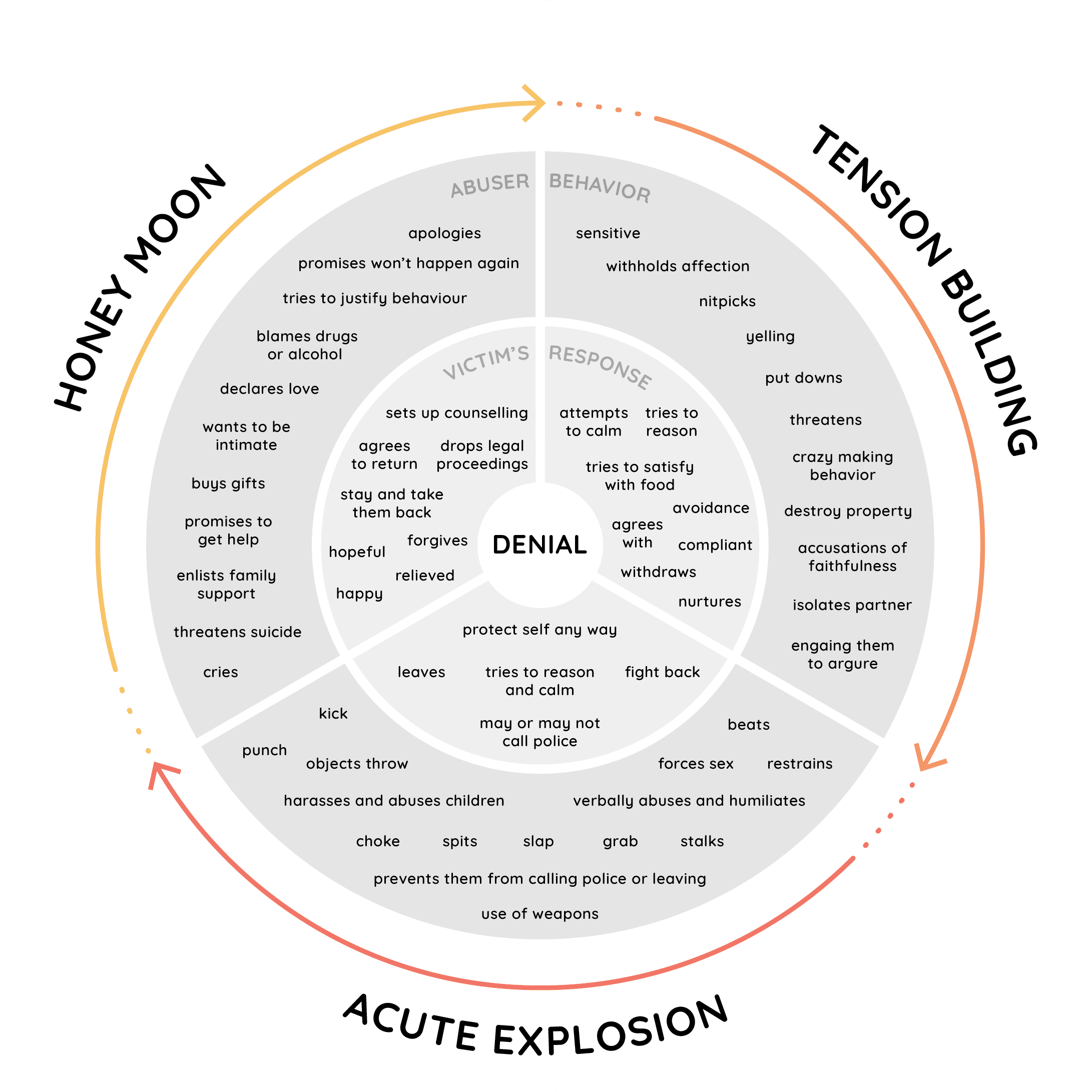
Threats of this magnitude almost never emerge in a vacuum. They follow a predictable "pathway to violence" that begins with radicalization and moves through research, planning, and logistics. The disruption of the plot mentioned by Tisch indicates a successful intervention during the "operationalization" phase—the period when an individual moves from rhetoric to acquiring the means for an attack.
The modern intelligence landscape faces a bottleneck in signal-to-noise ratios. Radicalized individuals often communicate in fragmented, encrypted, or coded language across decentralized platforms. To identify a credible threat, analysts must look for specific indicators of "Pre-Attack Preparation":
- Boundary Testing: Unusual surveillance of a facility or attempts to bypass minor security hurdles.
- Logistical Acquisition: The procurement of restricted materials or tactical gear that deviates from the individual's established consumer profile.
- Final Manifestos: The shift from general grievance to specific, time-bound intent.
The failure of an adversary to maintain operational security (OPSEC) during these phases provides the primary window for law enforcement intervention. When intelligence agencies "disrupt" a plot, they are essentially exploiting a lapse in the perpetrator's tactical discipline.
The Three Pillars of Defensive Hardening
To counter the threat profile faced by New York’s communal infrastructure, security strategy must be partitioned into three operational layers.
Layer 1: Perimeter Intelligence and Surveillance
This involves the deployment of high-definition optical sensors integrated with behavioral analytics. Rather than simple recording, modern systems utilize computer vision to detect anomalies—such as a vehicle circling a block at a specific frequency or an individual loitering in a high-risk zone during off-peak hours. The objective is to extend the "warning horizon" as far from the target's center as possible.
Layer 2: Access Control and Physical Redundancy
Physical security is measured by "Time-to-Breach." Every obstacle—shatter-resistant film on windows, reinforced entry points, or bollards to prevent vehicle ramming—is designed to buy seconds for the occupants and law enforcement. A building's architecture must be viewed through the lens of delay. If an attacker is forced to spend ninety seconds breaching a door instead of five, the probability of a successful neutralisation by responding units increases exponentially.
Layer 3: Human Element and Situational Awareness
Technology is a force multiplier, but it remains secondary to the "Human Sensor Network." Training communal staff and congregants in situational awareness transforms every individual into a data point. The "See Something, Say Something" protocol is often criticized for its simplicity, yet it remains the most effective method for detecting "Low-Signature" threats that evade digital surveillance.
The Logistics of Law Enforcement Interdiction
The transition from an identified threat to a physical arrest involves a high-stakes coordination of resources. In New York, this responsibility falls on a multi-jurisdictional framework involving the NYPD’s Intelligence and Counterterrorism Bureaus and federal partners.
The primary constraint in these operations is "Legal Thresholding." Law enforcement must wait until the perpetrator's actions constitute a definitive criminal attempt to ensure a successful prosecution, yet they cannot wait so long that the threat becomes imminent and uncontrollable. This "Intervention Gap" is where most strategic failures occur. If the arrest happens too early, the suspect may be released due to lack of evidence; if it happens too late, the intervention may occur during the attack itself.
Quantifying the Impact of Deterrence
Deterrence is notoriously difficult to measure because it is defined by the absence of an event. However, we can analyze the "Deterrence Gradient" by looking at the shift in attacker behavior. As high-profile targets in Manhattan or Brooklyn implement more rigorous security, adversaries often "shift down" to softer, less-protected targets in the periphery.
This creates a "Security Displacement" effect. A robust defense at a major synagogue may inadvertently redirect a threat toward a smaller, less-funded community center. A comprehensive strategy requires a "Tide-System" approach—where security funding and intelligence sharing are distributed across the entire communal ecosystem, rather than concentrated in a few high-visibility nodes.
Resource Allocation and the Cost of Vigilance
The financial burden of these security measures is non-trivial. Security is an operational tax on communal life. For many organizations, the cost function of maintaining a "Hardened State" includes:
- Capital Expenditures (CAPEX): Installation of cameras, gates, and reinforced glass.
- Operating Expenses (OPEX): Ongoing costs for private security personnel, monitoring services, and maintenance.
- Social Friction: The psychological toll on community members who must navigate an increasingly militarized environment to participate in religious or social life.
To optimize these costs, organizations are increasingly turning to "Tiered Readiness" models. In this framework, the baseline security posture is manageable, but the system can be rapidly scaled up in response to specific intelligence alerts or rising geopolitical tensions.
The Asymmetry of Modern Urban Conflict
We must recognize that the threat to the New York Jewish community, or any specific enclave, is a symptom of a broader shift toward decentralized, "leaderless" radicalization. The internet has democratized the ability to plan and execute high-impact strikes. Unlike traditional terrorist cells of the 20th century, which had centralized hierarchies that could be dismantled, modern threats often consist of "Lone Actor" nodes that are highly insulated and difficult to track.
This decentralization forces a shift from a "Search and Destroy" intelligence model to a "Resilience and Response" model. Since it is impossible to stop 100% of motivated actors from attempting a strike, the metrics of success must include the speed of recovery and the efficacy of the containment protocols.
[Image of a decentralized network vs. a centralized network]
Tactical Realignment for Communal Institutions
The immediate requirement for community leadership is a move away from reactive security—adding guards only after a threat is publicized—toward a proactive, data-driven posture. This involves several critical steps:
First, conduct a formal "Threat and Vulnerability Assessment" (TVA) that uses objective scoring to identify the weakest points in the physical and digital perimeter. This assessment should be updated annually or after any significant shift in the local threat landscape.
Second, integrate communal security networks with local law enforcement data feeds. Information silos are the primary enemy of rapid response. A suspicious person reported at one site must be instantly known to every other site within a five-mile radius.
Third, formalize the training of non-security staff. Every administrator, teacher, and volunteer should be proficient in "Active Threat Response" protocols. The objective is to turn the entire organization into an inhospitable environment for an adversary.
The long-term viability of high-density communal life in urban centers depends on this evolution. Security cannot be viewed as an external service that is "bought"; it must be an integrated component of organizational management. The goal is to create a "High-Friction Environment" where the logistical difficulty of an attack outweighs the perceived symbolic gain, effectively pricing the adversary out of the market for violence.